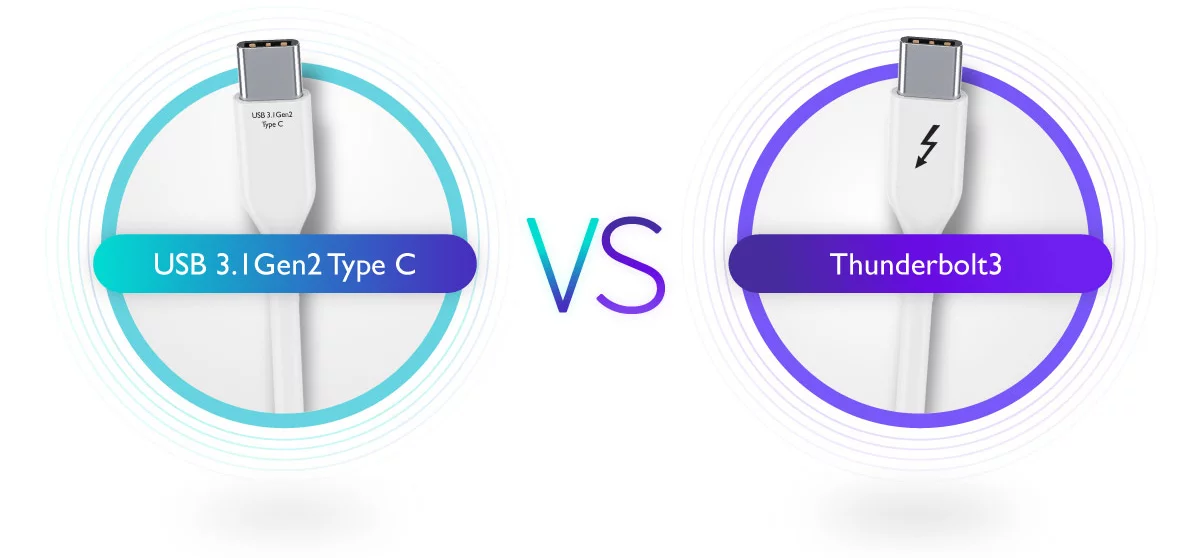
One of the reasons why users often get confused between Thunderbolt™ 3 and USB 3.1 Gen2 Type C is because the shape of both cables’ plugs looks exactly the same. However, the same plug is paired up with different transmission protocols. In other words, both cables are equipped with USB-C™ plugs but they each have […]
Category Archives: featured
As many of us stayed home in the past couple of years, you may be one of the people who invested in a laptop or desktop computer to use for online learning or work from home setup. After more than a year of use, have you experienced your computer slowing down? If your computer is […]
When it comes to gaming monitors, we often encounter the term “FreeSync” and how it improves gameplay, especially for FPS games. As the games and technology level up every year, so as this feature. So, let’s take our time to get to know what it does. WHAT IS FREESYNC FreeSync is AMD’s solution to eliminate […]
Do you access your mobile phone inside the MRT, LRT, Bus or even inside the elevator? If yes, then you might be vulnerable to visual hacking. It is the easiest and most low-tech form of information theft. It can be done by attackers by simply getting near you, and steal a glance at your screen. […]
WannaCry is also known as WannaCrypt, WanaCrypt0r 2.0, Wanna Decryptor has affected more than 70 countries in an unprecedented attack which was launched on 12th May 2017. Very recently Shadow brokers had leaked the US Spy agencies hacking tools and vulnerabilities and one of them was Eternal Blue exploit which relied on a SMB Exploit […]
An all-in-one point of sale solution that works as good as it looks, the Elo PayPoint already includes a cash drawer, receipt printer, MSR and barcode scanner. Explore the possibilities of this stylish POS using your choice of operating system. Elo PayPoint® for Windows® PayPoint for Windows integrates with all your back-office applications, leveraging the […]
The VZ-28s is designed with essential features and quality standards to ensure that users can communicate with ease. 40 Approved SRRS Channels Equipped with 40 Short Range Radio Service (SRRS) channels, users can easily pick-up this radio and operate it without the usual programming required of most radios. Compact Form Factor VZ-28s is designed with […]